Mac
Proprietary: Apple and Mcrosoft
Submitted by Roy Schestowitz on Friday 17th of June 2022 07:14:16 AM Filed under
-
Shared Photo Library
With iOS 16, it seems there will be options for family sharing, which sounds great now that we have five phones in our family snapping pictures and storing them in the cloud.
-
iPods are over
The first iPod was announced in October 2001, and most people agree that it revolutionized the way we listen to music nowadays. By that time, there were other music players, but no manufacturer was able to bring together an easy way for us to buy music - with some decent quality - and offer a well designed product. Obviously, some audiophile may disagree with my “decent quality” statement, but it really was for the average user that didn’t want (or need) to go deeper in all technicality in this regard.
-
House Armed Services chair calls national security software, systems 'too vulnerable' [iophk: Windows TCO]
“We’re talking about software systems that, you know, operate our missiles and our ships and everything, they just don’t, they are not as protected as they should be,” Smith said. “When it comes to cyber, protecting our systems, I think, is our greatest problem right now — even more so than our ability to exploit other people’s systems, though we certainly need to develop that capability as well.”
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 3056 reads
 PDF version
PDF version
Apple Disregards Security
Submitted by Roy Schestowitz on Tuesday 14th of June 2022 10:08:04 AM Filed under
-
Apple not ‘worried’ about the latest security attack on the M1 chip
A team of security researchers from MIT’s Computer Science and Artificial Intelligence Laboratory (MIT CSAIL) managed to defeat M1’s security measures, breaching the chip’s last line of security, the PAC (pointer authentication codes). The researchers developed a novel attack combining memory corruption and speculative execution, bypassing M1’s security. They found that the chip’s last line of security, often known as PAC (pointer authentication codes), can be breached through a hardware attack allowing attackers to gain access to the Mac.
-
Researchers discover a new hardware vulnerability in the Apple M1 chip
The M1 chip uses a feature called "Pointer Authentication," which acts as a last line of defense against typical software vulnerabilities. With Pointer Authentication enabled, bugs that normally could compromise a system or leak private information are stopped dead in their tracks. Now, researchers from MIT's Computer Science and Artificial Intelligence Laboratory have found a crack: their novel hardware attack, called "PACMAN" shows that Pointer Authentication can be defeated without even leaving a trace. Moreover, PACMAN utilizes a hardware mechanism, so no software patch can ever fix it.
-
MIT researchers warn of ‘PACMAN’ M1 flaw that can’t be patched
According to MIT CSAIL, since its PACMAN attack involves a hardware device, a software patch won’t fix the problem. The issue is a wider problem with Arm processors that use Pointer Authentication, not just Apple’s M1. “Future CPU designers should take care to consider this attack when building the secure systems of tomorrow,” Ravichandran wrote. “Developers should take care to not solely rely on pointer authentication to protect their software.” As a technological demonstration, PACMAN shows that pointer authentication isn’t completely foolproof and developers shouldn’t completely rely on it.
-
MIT Finds Apple M1 Vulnerability, Demos PACMAN Attack (Update)
The researchers say the PACMAN attack works across privilege levels, "implying the feasibility of attacking a PA-enabled operating system kernel."
When asked about the data exfiltration rate (i.e., how fast data can be stolen), the team tells Tom's Hardware, "It's hard to say since data exfiltration with this attack will be very dependent on the exact gadget used. Our proof of concept exploit takes 2.69 milliseconds per PAC guess (so worst-case 2.94 minutes per pointer). This may be longer in a fully integrated end-to-end attack."
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 2392 reads
 PDF version
PDF version
Have an old iPad lying around? You might be able to make it run Linux soon
Submitted by Roy Schestowitz on Thursday 2nd of June 2022 11:16:23 PM Filed under

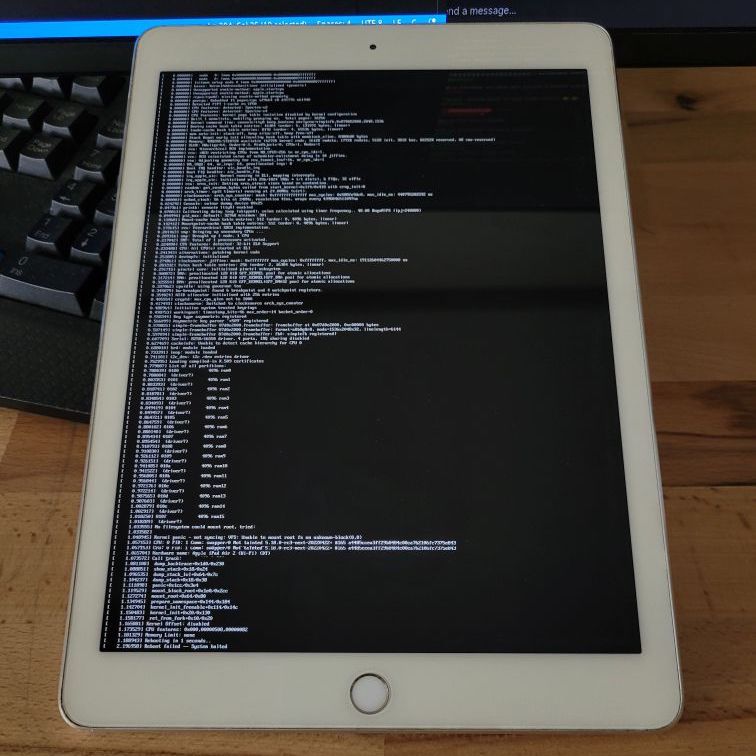
If you have a 2013- or 2014-era iPad sitting around unused because it's not getting updates from Apple anymore and has stopped running the apps you need, some developers are working on an alternative software solution for you. Developer Konrad Dybcio and a Linux enthusiast going by "quaack723" have collaborated to get Linux kernel version 5.18 booting on an old iPad Air 2, a major feat for a device that was designed to never run any operating system other than Apple's.
The project appears to use an Alpine Linux-based distribution called "postmarketOS," a relatively small but actively developed distribution made primarily for Android devices. Dybcio used a "checkm8" hashtag in his initial tweet about the project, strongly implying that they used the "Checkm8" bootrom exploit published back in 2019 to access the hardware. For now, the developers only have Linux running on some older iPad hardware using A7 and A8-based chips—this includes the iPad Air, iPad Air 2, and a few generations of iPad mini. But subsequent tweets imply that it will be possible to get Linux up and running on any device with an A7 or A8 in it, including the iPhone 5S and the original HomePod.
This isn't the only project devoted to running Linux on Apple's hardware. One project, Asahi Linux, has been dedicated to reverse-engineering support for the M1 chips in Apple's Macs and sending the patches upstream so that they can be integrated into the Linux kernel. Another, Project Sandcastle, has a build of Android up and running on an iPhone 7. Apps like iSH will give you a Linux shell running on top of iOS or iPadOS—not the same as running Linux on the hardware directly, but useful in some circumstances.
- 5 comments
 Printer-friendly version
Printer-friendly version- Read more
- 3394 reads
 PDF version
PDF version
Proprietary leftovers
Submitted by Roy Schestowitz on Sunday 15th of May 2022 12:49:01 PM Filed under

-
Google Docs crashed when fed 'And. And. And. And. And.'
Google Docs, the search giant's web-based word processing app, has been resuscitated after it was found choking on a series of conjunctions and other parts of speech.
-
Microsoft to nudge more users toward Azure Active Directory [Ed: How to fake "Azure" so-called 'market share' while worsening security]
-
Microsoft tests ‘Suggested Actions’ in Windows 11. Insiders: Can we turn it off? [Ed: Microsoft continues to rip off KDE]
-
Outlook bombards Safari users with endless downloads
Attention, Mac users who access Outlook with Safari: something's broken, and it's causing an empty TokenFactoryIFrame file to be downloaded every few seconds for as long as you remain there.
Microsoft hasn't said what's causing the problem, though it did acknowledge the ongoing blunder in this support message-board thread on Microsoft Answers. We understand this flood of downloads affects Safari on desktop Macs; it may also affect browsers on iOS using Safari's WebKit engine, such as Microsoft Edge on iPads.
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 2540 reads
 PDF version
PDF version
Proprietary: Apple and Microsoft (Product Shutdowns, Failures)
Submitted by Roy Schestowitz on Sunday 15th of May 2022 10:26:02 AM Filed under
-
The end of the iPod – last model available 'while supplies last' [Ed: It was always hype, branding, and perceived "class"; technically speaking, the competition was better and practically superior]
-
LinkedIn settles Dept of Labor charges it underpaid women [Ed: While Bill Gates flies on planes of Jeffrey Epstein and visits Epstein in prison Microsoft continues to abuse women. Microsoft loves to publicly brag about protecting women because, just like greenwashing, it makes business (marketing) sense.]
Microsoft's LinkedIn social network has agreed to settle allegations it systematically underpaid women in engineering, product, and marketing roles.
The US Department of Labor (DoL) on Tuesday announced the settlement on behalf of 686 female workers in California. The government said an evaluation conducted by DoL's Office of Federal Contract Compliance Programs found that between March 1, 2015, though March 1, 2017, LinkedIn failed to provide equal pay for women in its San Francisco and Sunnyvale, California, offices.
-
Warning: Windows update breaks authentication for some server admins
Microsoft is warning a security update may cause authentication failures for Windows domain controllers.
"After installing updates released May 10, 2022 on your domain controllers, you might see authentication failures on the server or client for services such as Network Policy Server (NPS), Routing and Remote access Service (RRAS), Radius, Extensible Authentication Protocol (EAP), and Protected Extensible Authentication Protocol (PEAP)," the IT goliath said in an advisory published Wednesday.
-
Jeffrey Snover claims Microsoft demoted him for inventing PowerShell [Ed: Microsoft did the same to the Minecraft pioneer]
PowerShell inventor Jeffrey Snover has aired some grievances about how his indispensable tool once got him demoted.
The Microsoft Technical Fellow discussed the incident in a weekend Twitter thread that started when controversial investor Peter Thiel discussed the virtues of courage.
"Courage is a key characteristic of future leaders and previous employees," Snover joked in response to Thiel's musings. He also asserted that "many people focus on getting their boss to pat them on the head rather than address problems."
-
Microsoft to ax Azure Video Analyzer in November [Ed: Microsoft also lays off Azure staff and shuts down some datacentres; it relies a lot on government bailouts (stealing from taxpayers]
Microsoft's Azure Video Analyzer service is being put out to pasture, with its termination notice arriving less than a year after the preview was unveiled at the company's 2021 Build event.
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 2399 reads
 PDF version
PDF version
Proprietary Debacles
Submitted by Roy Schestowitz on Wednesday 11th of May 2022 05:37:29 PM Filed under

-
Google Releases Security Updates for Chrome
Google has released Chrome version 101.0.4951.64 for Windows, Mac, and Linux. This version addresses vulnerabilities that an attacker could exploit to take control of an affected system.
-
CISA Adds One Known Exploited Vulnerability to Catalog [Ed: A correct headline would have said CISA Adds Microsoft Windows Known Exploited Vulnerability to Catalog]
CISA has added one new vulnerability to its Known Exploited Vulnerabilities Catalog, based on evidence of active exploitation. These types of vulnerabilities are a frequent attack vector for malicious cyber actors and pose significant risk to the federal enterprise. Note: to view the newly added vulnerability in the catalog, click on the arrow on the of the "Date Added to Catalog" column, which will sort by descending dates.
-
Critical F5 BIG-IP vulnerability exploited to wipe devices
A recently disclosed F5 BIG-IP vulnerability has been used in destructive attacks, attempting to erase a device's file system and make the server unusable.
-
10 iPod Competitors That Didn’t Make It
Some say it was overdue, some lament that it remains a missed opportunity, but the truth of the matter is, the iPod has left us, after years of neglect. The final iPod Touch was released in 2019, four years after the previous model, and essentially as a legacy model for a niche audience of people who don’t want modems in their phone-like devices—think hackers and the parents of young children. It was not what it was upon the device’s general release. But I want to take a step back with today’s Tedium to consider the many, many competitors to the digital music throne that Apple’s legacy device vanquished. There were many. And as the latest entry in my series of obscure things that “didn’t make it” or fell into modern-day obscurity, I’m covering 10.
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 2813 reads
 PDF version
PDF version
Proprietary Leftovers
Submitted by Roy Schestowitz on Wednesday 11th of May 2022 12:54:39 PM Filed under


-
Apple ends production of its iconic iPod
Apple announced Tuesday that it's discontinuing the iPod Touch — the last iPod model produced by the company — marking an end for the gadget that helped shape the music listening experience for 20 years.
-
Apple discontinues the iPod after 20 years
The iPod Touch going away marks the end of an era. As Apple notes, it introduced the first iPod “over 20 years ago.” The original FireWire-equipped model acted as just a portable music player, and Apple made models that were pretty much exclusively for listening to audio up until 2017, when it discontinued the iPod Nano and Shuffle. While the iPod Touch has been embraced by some iPod enthusiasts as the new classic music player, it also found a following for those who wanted an iPhone-like experience but didn’t actually need a phone
-
Microsoft May 2022 Patch Tuesday fixes 7 critical vulnerabilities, 67 others
-
Attribution of Russia’s Malicious Cyber Activity Against Ukraine [iophk: Windows TCO]
Today, in support of the European Union and other partners, the United States is sharing publicly its assessment that Russia launched cyber attacks in late February against commercial satellite communications networks to disrupt Ukrainian command and control during the invasion, and those actions had spillover impacts into other European countries. The activity disabled very small aperture terminals in Ukraine and across Europe. This includes tens of thousands of terminals outside of Ukraine that, among other things, support wind turbines and provide Internet services to private citizens.
-
Russia seems to be co-ordinating cyber-attacks with its military campaign [iophk: Windows TCO]
The number of Russian cyber-operations has doubled every month since December, when 15 were reported. This only includes attacks that Microsoft was able to detect in its own networks—the true number is likely to be higher. But because the Russians are conducting disruptive attacks, they are much more likely to be found out than pure espionage, such as Chinese intelligence gathering against America, reckons Benjamin Read, director of espionage analysis at Mandiant, a cybersecurity firm.
-
No kidding, Microsoft now charges firms to tackle Windows ransomware [iophk: Windows TCO]
I kid you not. No other operating system suffers ransomware attacks, though helpful security experts try to spread the burden a bit, and suck up to the big M, by claiming they have seen similar malware for Linux and the Mac.
But no attack in which a ransom has been demanded and a company put out of operation for a while has involved anything other than Windows.
This kind of money making is in keeping with Microsoft's culture; the one thing the company possesses in spades is chutzpah. It is absolutely brazen in its bid to make money off something which its own products allow to happen.
-
Risky Biz News: Costa Rica declares national emergency after ransomware attack [iophk: Windows TCO]
The attack hit the Central American state right in the middle of its presidential transition, with former president Carlos Alvarado Quesada telling journalists on April 21 that the attack had destabilized the government in a period of transition.
-
Costa Rica’s new president declares state of emergency after Conti ransomware attack [iophk: Windows TCO]
The newly-inaugurated president of Costa Rica – Rodrigo Chaves – declared a state of emergency due to a devastating ransomware attack launched by the Conti group.
Following his swearing-in ceremony on Sunday, Chaves held his first government council, where he announced a national emergency and attributed it to the attack’s effects on the Ministry of Finance, which has been hit hardest by the attack.
-
US State Department announces $10 million bounty after Costa Rica ransomware attack [iophk: Windows TCO]
The US State Department says the attack “severely impacted the country’s foreign trade by disrupting its customs and taxes platforms” and offers “up to $10 million for information leading to the identification and/or location” of the organizers behind Conti. The US government is also offering $5 million for information “leading to the arrest and/or conviction of any individual in any country conspiring to participate in or attempting to participate” in a Conti-based ransomware attack.
-
Costa Rican president begins tenure with ransomware national emergency declaration [iophk: Windows TCO]
President Rodrigo Chaves Robles, who began a four-year term as president Sunday after winning the country’s April 4 election, signed the declaration on May 8 as one of his first official acts, according to local news outlet Amelia Rueda. The executive decree reads, in part, that Costa Rica is “suffering from cybercriminals, cyberterrorists” and that the decree allows “our society to respond to these attacks as criminal acts.”
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 2682 reads
 PDF version
PDF version
KDE Connect Arrives on iPhone and iPad For Linux Fans
Submitted by Roy Schestowitz on Monday 9th of May 2022 10:13:09 PM Filed under
-
KDE Connect Arrives on iPhone and iPad For Linux Fans
KDE Connect has been around for years as a companion Android app for connecting to Linux PCs, similar to Microsoft Link to Windows (formerly “Your Phone”). Now there’s finally a KDE Connect app for iPhone and iPad.
KDE Connect has quietly appeared on the Apple App Store for iPhone and iPad, seemingly without an official announcement (at least so far). Just like the Android version, it connects to a Linux PC running the KDE Connect application to a phone or tablet. You can then synchronize your clipboard across desktop and mobile, share files and links, and run commands on a PC from a phone. You can also use an iPhone as a virtual touchpad or presentation remote for a linked PC.
-
KDE Connect is Now Available for iPhone & iPad - OMG! Ubuntu!
An official KDE Connect mobile client is now available on the Apple App Store.
The addition of this official iOS app means folks with an iPhone and/or iPad can benefit from a deeper set of integration between their mobile devices and their Linux desktop.
- 5 comments
 Printer-friendly version
Printer-friendly version- Read more
- 5762 reads
 PDF version
PDF version
Proprietary Software Leftovers
Submitted by Roy Schestowitz on Saturday 7th of May 2022 10:59:22 PM Filed under

-
Microsoft Tells Users to Uninstall Windows 11 Update That Causes Apps to Crash [Ed: Windows eXPeriment]
-
Microsoft advises users to uninstall Windows 11 update [Ed: This might be a plagiarism site, but it's funny nonetheless]
-
CloudCasa by Catalogic to Feature Cyber-Resilient Kubernetes Backups at KubeCon + CloudNativeCon Europe 2022
-
TurboTax will pay $141 million for scamming taxpayers
TurboTax will pay $141 million to residents in every state and Washington D.C. for misleading claims that its tax preparation services are free, New York Attorney General Letitia James announced Wednesday.
Under the agreement, a total of 4.4 million taxpayers who used TurboTax's free edition for tax years 2016 through 2018 will get a direct payment of approximately $30 for each year. These users were told that they had to pay to file, even though they were eligible to file for free using the IRS Free File program, which the Intuit withdrew from in 2021. In New York, 176,000 residents who were "tricked into paying to file their federal tax return" will receive a total of more than $5.4 million.
-
MacOS Server, Adieu
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 2743 reads
 PDF version
PDF version
Proprietary Software Leftovers
Submitted by Roy Schestowitz on Tuesday 22nd of March 2022 03:58:29 PM Filed under


-
White House warns Russia prepping possible cyberattacks against US [iophk: Windows TCO]
The White House on Monday urged private companies to bolster their cyber defenses, citing evolving intelligence suggesting the Russian government is exploring “options for potential cyberattacks” targeting U.S. critical infrastructure.
-
Biden tells CEOs they have 'patriotic obligation' to guard against Russian cyberattacks [iophk: Windows TCO]
President Biden on Monday called on top business executives to build up their companies' capacity to deal with potential cyberattacks from Russian President Vladimir Putin amid the invasion of Ukraine.
-
Apple services are down for some users
The outage impacted some apps and people differently. In some cases, an app like the App Store would load but would hang or wouldn’t let you download an app. In other cases, the app won’t load altogether. It’s not clear what caused the outage and an Apple spokesperson declined to comment.
-
First Samsung breach, now Microsoft: Lapsus$ makes bold claim
The claims by Lapsus$, a group that appears to be based in Brazil, are being taken seriously because its earlier claims about Samsung, and also Nvidia, were proved to be true.
Additionally, Microsoft has not made any categorical denial of the claim that its Azure DevOps servers were breached and data stolen.
-
Microsoft may be the latest victim of Lapsus$
The South American-based data extortion hacking group Lapsus$ has allegedly gained access to Microsoft's Azure DevOps source code repositories and stolen data from the company.
Unlike other cybercriminal groups which deploy ransomware on the devices of their victims, Lapsus$ instead prefers to target the source code repositories of large tech companies. After stealing their proprietary data, the group then tries to ransom it back to the companies themselves for millions of dollars.
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 2754 reads
 PDF version
PDF version
More in Tux Machines
- Highlights
- Front Page
- Latest Headlines
- Archive
- Recent comments
- All-Time Popular Stories
- Hot Topics
- New Members
digiKam 7.7.0 is released
After three months of active maintenance and another bug triage, the digiKam team is proud to present version 7.7.0 of its open source digital photo manager. See below the list of most important features coming with this release.
|
Dilution and Misuse of the "Linux" Brand
|
Samsung, Red Hat to Work on Linux Drivers for Future Tech
The metaverse is expected to uproot system design as we know it, and Samsung is one of many hardware vendors re-imagining data center infrastructure in preparation for a parallel 3D world.
Samsung is working on new memory technologies that provide faster bandwidth inside hardware for data to travel between CPUs, storage and other computing resources. The company also announced it was partnering with Red Hat to ensure these technologies have Linux compatibility.
|
today's howtos
|







.svg_.png)
 Content (where original) is available under CC-BY-SA, copyrighted by original author/s.
Content (where original) is available under CC-BY-SA, copyrighted by original author/s.

Recent comments
47 weeks 1 day ago
47 weeks 2 days ago
47 weeks 2 days ago
47 weeks 2 days ago
47 weeks 2 days ago
47 weeks 2 days ago
47 weeks 2 days ago
47 weeks 3 days ago
47 weeks 3 days ago
47 weeks 3 days ago